

Yeah, we’ll get into that right after we solve SQL injection vulnerabilities. Don’t rush us.


Yeah, we’ll get into that right after we solve SQL injection vulnerabilities. Don’t rush us.


Sway-wm used to be spawnable as a child window, not sure if that is still possible.
I think you should also be able to get multiple ctrl-alt-fX graphical sessions.
I’ll come back and update this comment when I get to my PC and give this a try.
Edit: seem Max-P’s comment.


Sounds like their strategy from 10 years ago.


That’s just what CMG claimed to have.
But to be useful for an advertising network, it kinda needs to be installable on everything. And if it failed to suppress the mic LED on a single device, it would be very easily noticed?
I think its better to keep your gateway basic, and run extra services on a separate raspi or similar. Let your router/gateway focus on routing packets.
Openwrt can run Adguard, and as long as your gateway can run docker, you can probably get pihole working.


Sure, except we are defenceless to the rampant dropbears. /s
Australia is a funny example for gun control. Yanks seem to think we have no guns at all, but the reality is that as long as you are mentally sound and store your guns safely, they aren’t that hard to get.


Any idiot and chatgpt could knock up an overt always listening app in an afternoon. I have no doubt shady apps already can do this. Its not hard or expensive. (Backend storage and audio processing costs are a different kettle of fish, and I think those make this fairly prohibitive as well, but that’s a funding problem, not a technical problem.)
But as soon as they make the claim that it doesn’t trigger the microphone LED on iOS and Android, across all devices, then that’s a “technically hard” problem. That’s multiple zero days across multiple devices. Its just not feasable for an ad tech firm. They would never be able to recoup that investment.
I’m happy to be proven wrong, but so far all the researchers in the world have found nothing.
So I’m attributing near 0% chance that anyone outside of nation states have the later tech (device agnostic covert audio recording).


The capabilities TLAs have costs hundreds of millions of dollars to develop, and once caught, are worthless. TLAs are extremely careful with their toys to avoid them being caught.
This Adtech company is claiming to have something at that level, which they are deploying everywhere. If it existed, it would have been found the day after they announced it, the security researcher industry would be all over it. They are very intelligent people who do understand those devices inside and out, if it existed they would find it. Remember, these are the same researchers who frequently out actual TLA tools.
You can’t prove a negative, so it definitely is a probability thing, but I put the probability at basically 0 that they have what they claim.


The capability they were claiming to have would make a three letter agency very excited. If they truely had the ability to listen to your microphone, transparently without notifying the user, they could sell that tech to every regime that wants to snoop on people, for millions of dollars.
Instead they claim to be using it for Ad-tech, where if it existed, would make it trivial to discover and flag as malware.
Apple and Google would also be very keen to find and squash whatever loophole let’s them record without showing the notification.
Its just an extraordinary claim, which if true would have been exposed/validated by security researchers long ago.


Not disputing the three letter agencies, but there is zero evidence that that ad company ever had the tech or ability. They were/are just full of shit.


This was pretty clear when observing the output of tldrbot. It would just randomly select paragraphs, ignoring surrounding context, and call it a summary.


Yup, I mispoke, but essentially yes, they could be DC, but at a significantly higher voltage than 12v DC.
Some appliances use the AC frequency to timekeep as well, but given almost all appliances have microcontrollers now, that hardly matters anymore.
I would have thought DC motors would have worse longevity, given they have a wear surface due to the split ring commutator? Unless they are talking about ESC DC motors?


All the small stuff is low voltage DC, but just about every appliance requires AC (ovens, dishwashers, kettles, toasters, washing machines, aircon). Running an oven on 12v DC would be insane.


I kinda like the keyboard shortcuts for i3/sway, but wish there was some level of mouse integration/polish like gnome. Will try forge, thanks!


Tegra was used in android tablets, I had a couple. Not sure what the licence status was, but it was supported in cyanogen, so they must have had to make some changes to the kernel for that?
Certainly some of the stuff the upstreamed was to support their drivers, but they would have also been working on other more general things to support their super computers and other HPC stuff.
They also had a chipset for intel motherboards (which I can’t find anything about), which may have had some work required?
I don’t really know exactly the scope of all the work, but they have been in the top 20 companies for kernel development for a long time, and I assuming it can’t just be supporting their own drivers.
Its hard to find the stats, but from here: https://bootlin.com/community/contributions/kernel-contributions/ you can click through and get breakdowns per kernel release: https://web.archive.org/web/20160803012713/remword.com/kps_result/3.8_whole.html


My memory is fuzzy, but they have had their tegra SOC since the 2000s, and somewhat more recently they have been a big player in data center networking.
And ever since CUDA became a thing they have been a big name in HPC and super computers, which is usually Linux based.
So they have done a lot of behind the scenes Linux work (and possibly BSD?).


Nvidia have been big kernel contributers for a long time, even before the “fuck you nvidia” thing. They hold their graphics driver close to their chest, but have done a lot of other work for the kernel.
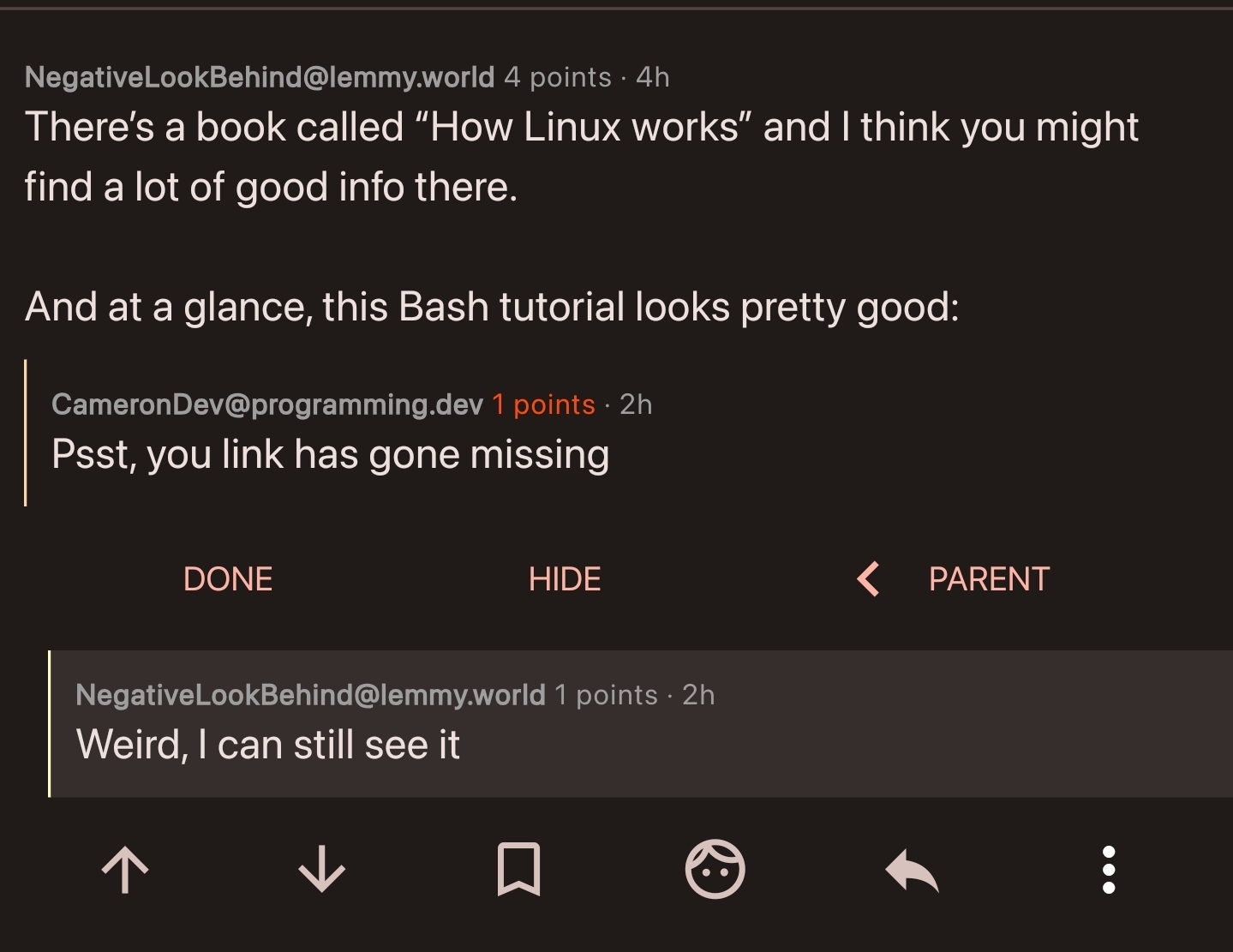
Very weird. Maybe its the client. Can’t see it in the browser either
Ah, I see whats happened, you didnt put anything in the square brackets:
[](https://www.freecodecamp.org/news/shell-scripting-crash-course-how-to-write-bash-scripts-in-linux/)
should be:
[Cool Tutorial](https://www.freecodecamp.org/news/shell-scripting-crash-course-how-to-write-bash-scripts-in-linux/)
resulting in:
The malware argument is a bit weak, if your router is vulnerable to something it’ll likely be found and pwnd in a matter of minutes, so turning it off a night won’t really save you. And once a patch is released, it’ll be reverse engineered in a few hours/days, so ideally you want patches as soon as they are released.
Using your own device is usually a good idea anyway, telco stuff is usually pretty mediocre. And as soon as your device is slightly custom, it becomes a less valuable target.